The global market for the Internet of things (IoT) reached $100 billion in revenue for the first time in 2017, and forecasts suggest that this figure will grow to around $1.6 trillion by 2025.
With such a prognosis, the technology is predicted to step far ahead than anyone can possibly imagine. But with the rise in popularity of IoT devices, there will be a rise in IoT app development as well as security challenges and issues.
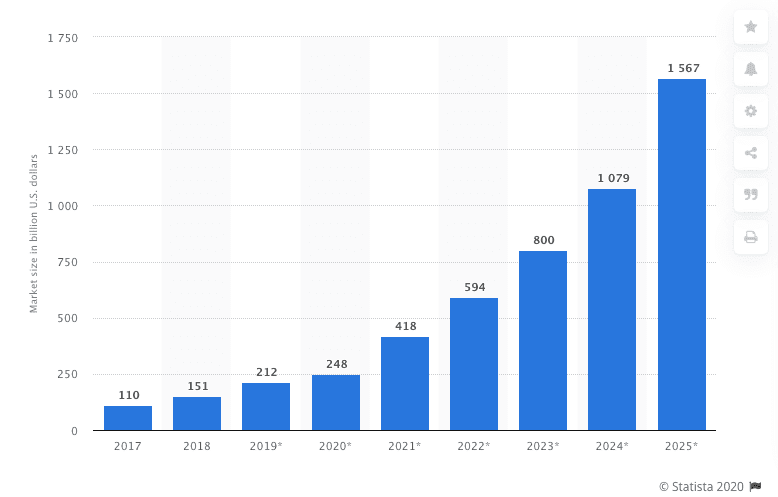
Source: Statista
In October 2016, a hacker found a vulnerability in a specific model of security cameras. Nearly 300,000 Internet of Things (IoT) video recorders started to attack multiple social network websites and brought down Twitter and other high-profile platforms for almost two hours. This attack is just an example of what can happen to IoT devices with poor security.
In October 2016, a hacker found a vulnerability in a specific model of security cameras. Nearly 300,000 Internet of Things (IoT) video recorders started to attack multiple social network websites and brought down Twitter and other high-profile platforms, for almost two hours.
This attack is just an example of what can happen to IoT devices with poor security.
It is not only video cameras, but anything with an internet connection, from a refrigerator, smart locks, thermostats, lightbulbs, vehicles, and even smart toys.
Using them always poses IoT security challenges and risks to overcome.
IoT Security Challenges
Now, it is not only us with our computers, but there are also “things” that interact with the Internet without our intervention. These “things” are continually communicating with the Internet, a fridge sending an update of the food inside or our vehicle transmitting messages to the mechanic to inform its oil levels.
IoT is wonderful in many ways. But unfortunately, technology has not matured yet, and it is not entirely safe. The entire IoT environment, from manufacturers to users, still have many security challenges of IoT to overcome, such as:
- Manufacturing standards
- Update management
- Physical hardening
- Users knowledge and awareness
Top IoT Security Risks
Returning to what happened in 2016, the lack of compliance on the part of IoT manufacturers led to weak and unprotected passwords in some IoT video cameras, which, in turn, led to one of the most damaging botnet attacks, the Mirai malware. There are many IoT security threats, but we will be highlighting the most important.
The following security issues with IoT can be classified as a cause or effect.
1) Lack of Compliance on the Part of IoT Manufacturers
New IoT devices come out almost daily, all with undiscovered vulnerabilities.
The primary source of most IoT security issues is that manufacturers do not spend enough time and resources on security.
For example, most fitness trackers with Bluetooth remain visible after the first pairing, a smart refrigerator can expose Gmail login credentials, and a smart fingerprint padlock can be accessed with a Bluetooth key that has the same MAC address as the padlock device.
This is precisely one of the biggest security issues with IoT. While there is a lack of universal IoT security standards, manufacturers will continue creating devices with poor security. Manufacturers that started to add Internet connection to their devices do not always have the “security” concept as the crucial element in their product design process.
The following are some security risks in IoT devices from manufacturers:
- Weak, guessable, or hard-coded passwords
- Hardware issues
- Lack of a secure update mechanism
- Old and unpatched embedded operating systems and software
- Insecure data transfer and storage

A smart thermostat
2) Lack of User Knowledge & Awareness
Over the years, Internet users have learned how to avoid spam or phishing emails, perform virus scans on their PCs, and secure their WiFi networks with strong passwords.
But IoT is a new technology, and people still do not know much about it. While most of the risks of IoT security issues are still on the manufacturing side, users and business processes can create bigger threats. One of the biggest IoT security risks and challenges is the user’s ignorance and lack of awareness of the IoT functionality. As a result, everybody is put at risk.
Tricking a human is, most of the time, the easiest way to gain access to a network. A type of IoT security risk that is often overlooked is social engineering attacks. Instead of targeting devices, a hacker targets a human, using the IoT.
Social engineering was used in the 2010 Stuxnet attack against a nuclear facility in Iran. The attack was directed to industrial programmable logic controllers (PLCs), which also fall into an IoT device category. The attack corrupted 1,000 centrifuges and made the plant explode. It is believed that the internal network was isolated from the public network to avoid attacks, but all it took was a worker to plug a USB flash drive into one of the internal computers.
3) IoT Security Problems in Device Update Management
Another source of IoT security risks is insecure software or firmware. Although a manufacturer can sell a device with the latest software update, it is almost inevitable that new vulnerabilities will come out.
Updates are critical for maintaining security on IoT devices. They should be updated right after new vulnerabilities are discovered. Still, as compared with smartphones or computers that get automatic updates, some IoT devices continue being used without the necessary updates.
Another risk is that during an update, a device will send its backup out to the cloud and will suffer a short downtime. If the connection is unencrypted and the update files are unprotected, a hacker could steal sensitive information.
4) Lack of Physical Hardening
The lack of physical hardening can also cause IoT security issues. Although some IoT devices should be able to operate autonomously without any intervention from a user, they need to be physically secured from outer threats. Sometimes, these devices can be located in remote locations for long stretches of time, and they could be physically tampered with, for example, using a USB flash drive with Malware.
Ensuring the physical security of an IoT device begins with the manufacturer. But building secure sensors and transmitters in the already low-cost devices is a challenging task for manufacturers nonetheless.
Users are also responsible for keeping IoT devices physically secured. A smart motion sensor or a video camera that sits outside a house could be tampered with if not adequately protected.
5) Botnet Attacks
A single IoT device infected with malware does not pose any real threat; it is a collection of them that can bring down anything. To perform a botnet attack, a hacker creates an army of bots by infecting them with malware and directs them to send thousands of requests per second to bring down the target.
Much of the uproar about IoT security began after the Mirai bot attack in 2016. Multiple DDoS (Distributed Denial of Service) attacks using hundreds of thousands of IP cameras, NAS, and home routers were infected and directed to bring down the DNS that provided services to platforms like GitHub, Twitter, Reddit, Netflix, and Airbnb.
The problem is that IoT devices are highly vulnerable to Malware attacks. They do not have the regular software security updates that a computer has. So they are quickly turned into infected zombies and used as weapons to send incredibly vast amounts of traffic.
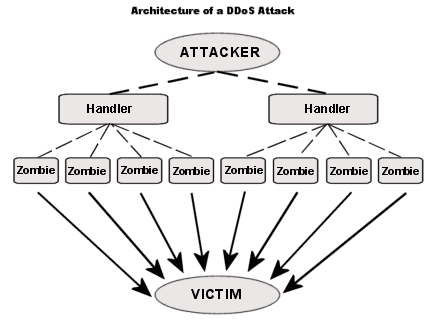
What is more, a botnet can pose a security threat for electrical grids, manufacturing plants, transportation systems, and water treatment facilities, which can threaten big groups of people. For example, a hacker could trigger a cooling and heating system at the same time, creating spikes on the power grid; in case of a big-scale attack, hackers can create a nation-wide power outage.
6) Industrial Espionage & Eavesdropping
If hackers take over surveillance at a location by infecting IoT devices, spying might not be the only option. They can also perform such attacks to demand ransom money.
Thus, invading privacy is another prominent IoT security issue. Spying and intruding through IoT devices is a real problem, as a lot of different sensitive data may be compromised and used against its owner.
On a basic level, a hacker might want to take over a camera and use it for spying. Still, one should not forget that many IoT devices record user information, whether it is health equipment, smart toys, wearables, etc. On an industrial level, a company’s big data can be collected by hackers to expose sensitive business information.
Some countries are starting to ban specific IoT devices with security problems. For example, the interactive IoT doll with a Bluetooth pin, which gave access to the toy’s microphone and speaker to anyone within the 25-30 meter radius. The doll was labeled as an espionage device and was banned in Germany.
7) Highjacking Your IoT Devices
Ransomware has been named as one of the nastiest malware types ever existed. Ransomware does not destroy your sensitive files — it blocks access to them by way of encryption. Then, the hacker who infected the device will demand a ransom fee for the decryption key unlocking the files.
Here is how a ransomware notice looks like:
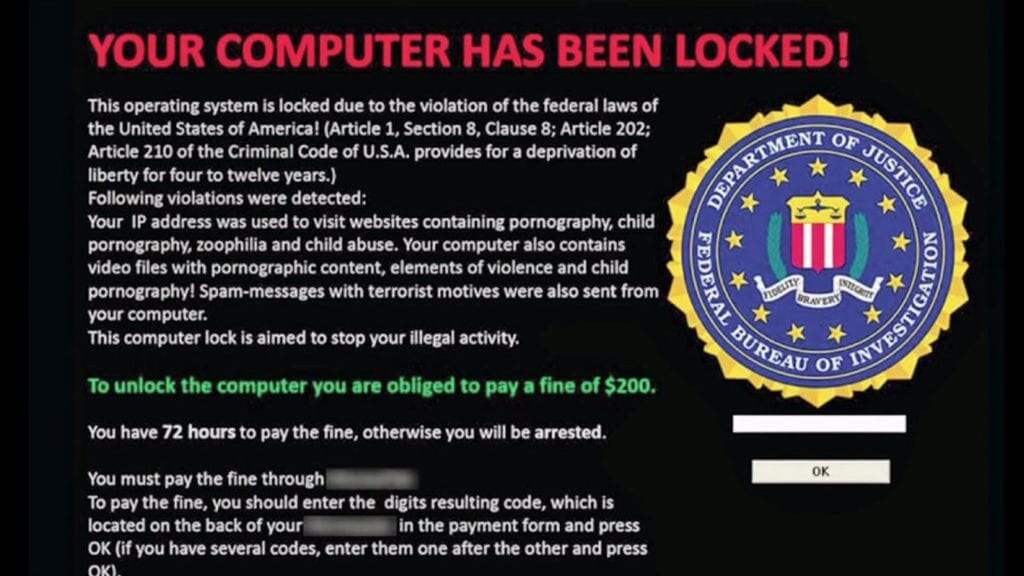
Ransomware is evolving, and IoT devices with poor security can become targets as well.
Just before the Trump inauguration speech, about 70% of the Washington DC surveillance cameras were infected with ransomware, leaving the police without the ability to record for several days.
The cases of IoT devices being infected with ransomware are rare, but the concept is quickly becoming a trend in the black hat hacker world. Still, wearables, healthcare gadgets, smart homes, and other smart devices and ecosystems might be at risk in the future.
Here, there is good news, and there is bad news. While this malware might not have valuable data to lock down because most IoT information is stored in the cloud, it can lock down the entire device’s functionality. Imagine that your vehicle will not start unless you pay a ransom fee — or your house is locked down, with the thermostat set to the maximum.
8) Data Integrity Risks of IoT Security in Healthcare
With IoT, data is always on the move. It is being transmitted, stored, and processed.
Most IoT devices extract and collect information from the external environment.
It can be a smart thermostat, HVAC, TVs, medical devices. But sometimes these devices send the collected data to the cloud without any encryption.
As a result, a hacker can gain access to a medical IoT device, gaining control over it and being able to alter the data it collects. A controlled medical IoT device can be used to send false signals, which in turn can make health practitioners take actions that may damage the health of their patients.
For example, a hacked medical IoT device can report a fully charged battery to the maintenance station while, in reality, the battery is about to die. Worse, there are risks of IoT security in healthcare devices like pacemakers or the ones making the insulin shots. The vulnerabilities found on St. Jude Medical’s implantable cardiac gave access to hackers, enabling them to alter the pacing or shocks, or even worse, deplete the battery.
9) Rogue IoT Devices
We might already know about the rapid growth of the number of IoT devices, which is predicted to reach 18 billion by 2022, according to Ericsson. The problem with this number of devices arises not only in the BYOD (Bring-Your-On-Devices) approach in enterprises but also in home networks.
One of the most significant IoT security risks and challenges is being able to manage all our devices and close the perimeter.
But rogue devices or counterfeit malicious IoT devices are beginning to be installed in secured networks without authorization. A rogue device replaces an original one or integrates as a member of a group to collect or alter sensitive information. These devices break the network perimeter.
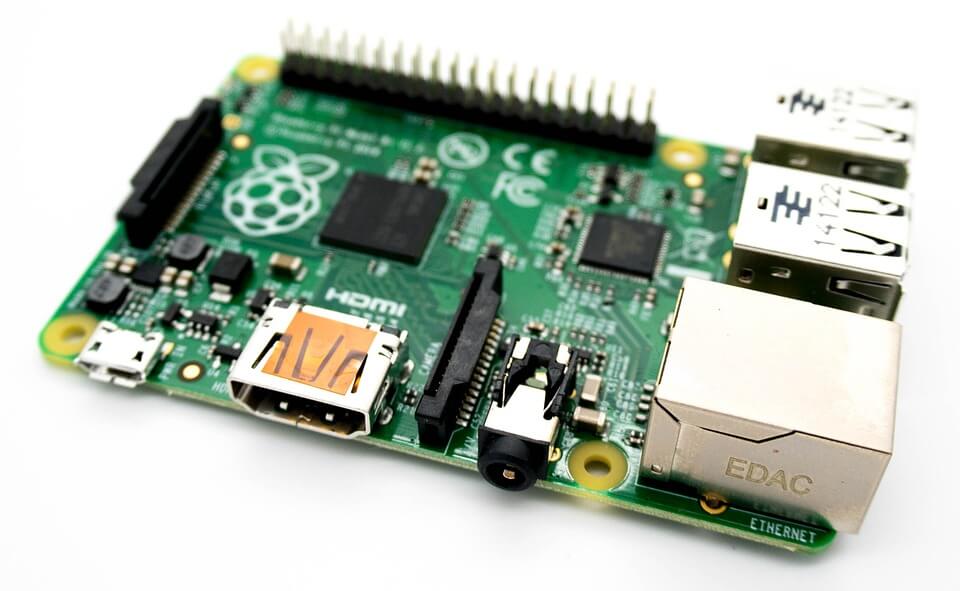
Raspberry Pi board
Example of rouge IoT devices can take the form of the Raspberry Pi, or WiFi Pineapple. These can be turned into a rogue AP (Access Point), thermostat, video camera, or MITM (Man in the Middle) and intercept incoming data communications unbeknownst to users. Other variations of rogue devices may also emerge in the future.
Interestingly, the horror movie “Child’s Play” was inspired by the concept and can serve as a curious example. In the movie, controlling other devices in a smart home system, Chucky is a rogue IoT device that has become a high-level threat to people’s lives.
10) Cryptomining with IoT Bots
Mining cryptocurrency demands colossal CPU and GPU resources, and another IoT security issue has emerged due to this precondition — crypto mining with IoT bots. This type of attack involves infected botnets aimed at IoT devices, with the goal not to create damage, but mine cryptocurrency.
The open-source cryptocurrency Monero is one of the first ones to be mined using infected IoT devices, such as video cameras. Although a video camera does not have powerful resources to mine cryptocurrency, an army of them does.
IoT botnet miners pose a great threat to the crypto market, as they have the potential to flood and disrupt the entire market in a single attack.
Summary
After the Mirai attack, people realized that any device connected to the Internet is a potential ally for an army of bots. But that was only the beginning.
For now, IoT and security are still not found in the same place. There are still many risks and security challenges of IoT now — and more will inevitably emerge in the coming years.
The more variations of IoT devices we see out there, the more complex IoT security problems will become. International organizations and governments will need to create universal IoT standards to control the security in cities, homes, locations like nuclear plants, the manufacturing process, and other areas and locations.
We have seen the emergence of IoT as a trend in the last few years. There are smart devices coming out that we never thought needed an Internet connection: smart toothbrushes, beauty mirrors, tables, pillows, beds, and the list continues to grow. The world is turning into a network of objects collecting our personal, sensitive information.
We can only imagine the amount of important data hackers could steal from those IoT devices if they do not have proper security. So, the top IoT security threats listed above are just the beginning. If we want our devices smart, we need them to be secure as well.
We, at Intellectsoft, empower companies and their workforce with cutting-edge transformative solutions and data-driven insights. Are you and your organization ready to shift the mindsets and get the most out of innovations?
Talk to our experts and find out more about the topic and how your business or project can start benefiting from it today!